Threat Talks
Recent Episodes
The Agent Problem
Find Threat Talks onThe Lethal Triangle: Why Your Agent Is a Breach Vector Agentic AI has put autonomous software inside your systems, with your permissions, against the data you’re paid to protect, and most organizations don’t yet have a security model for it. In...
Your Sales Team is now a Developer
Your team is already using AI coding agents – whether you know it or not. Find out what that means for your security, and what to do about it.
The Hidden Risk of Your Infrastructure
Find Threat Talks onThe Hidden Risk of Your Infrastructure Nation state actors have been targeting critical infrastructure for years, and most organizations are not as prepared as they think. The risk is not just about who is trying to get in. It is about what is...
America Just Changed the Rules of Cyber War
Find Threat Talks onAmerica Just Changed the Rules of Cyber War America just released a new national cyber strategy. And it is not just about defense anymore – it is about preparing for what is coming. In this episode of Threat Talks, Lieuwe Jan Koning, Co-founder and...
The EU is forcing the conversation
Data sovereignty in the cloud is more than location. Learn how control, dependency, and AI data governance shape real risk.
Europe vs China vs US: Who Controls Your Tech?
How the EU Cybersecurity Act is reshaping supply chain security as reliance on US and Chinese suppliers exposes hidden cybersecurity risks.
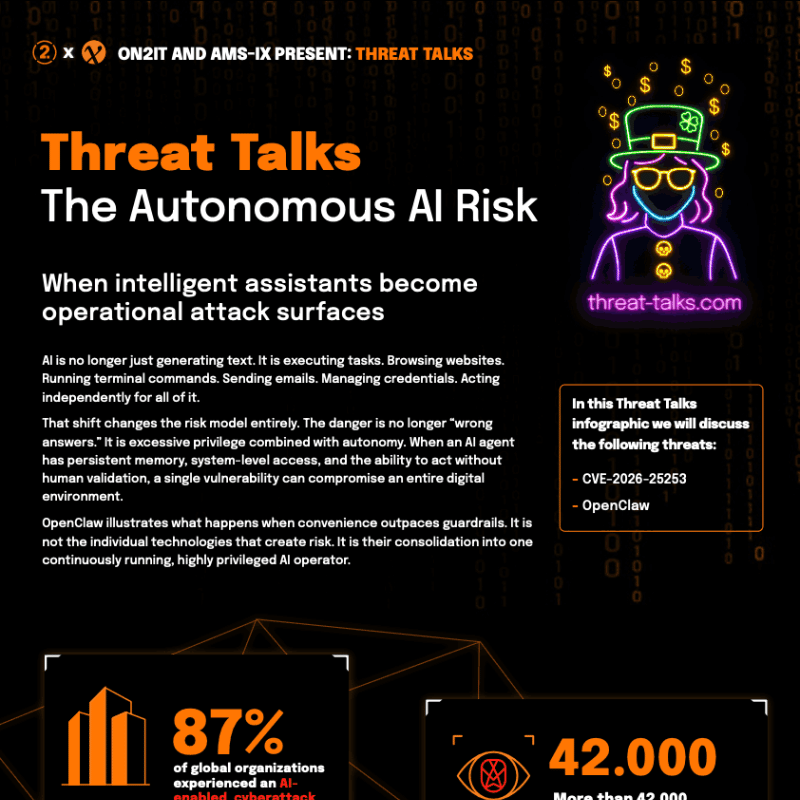
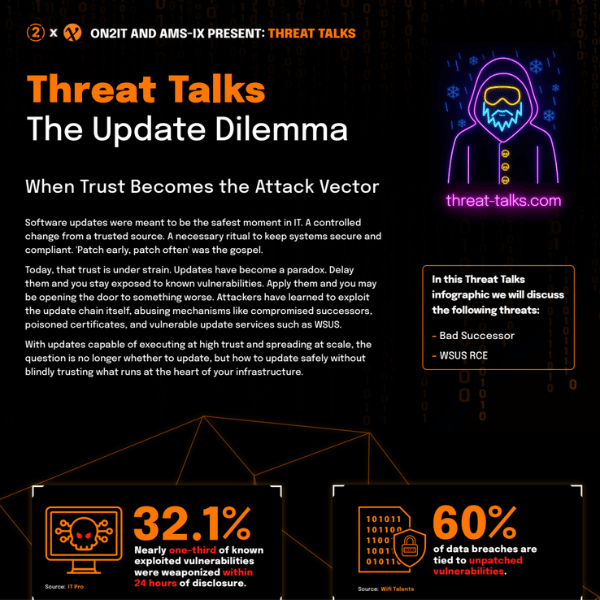
Cybersecurity Infographics
JOIN THE CYBERSECURITY CONVERSATION
Subscribe to Threat Talks for in-depth explorations of recent cybersecurity threats and trends, with exclusive insights and expert perspectives.